GotoSSH suggests "We act as a Center-male amongst your Net browser and the SSH session for your server device. "
Trusted: TCP guarantees that details might be shipped as a way and with out glitches. This would make TCP far more ideal for programs that demand dependable knowledge transmission.
in between the endpoints is not possible because of network constraints or security procedures. With its a variety of use
Unreliable: UDP will not promise that facts will be shipped to be able or without mistakes. This can be a downside for apps that involve responsible details transmission.
In this instance I’m also adding a DNS file to proxy it via Cloudflare servers in the event of IP handle blacklist.
When virtual private networks (VPNs) have been first conceived, their major functionality was to create a conduit involving faraway computer systems so that you can aid remote accessibility. And we were being able to accomplish it with traveling colors. Having said that, in later years, Digital personal networks (VPNs) were progressively commonly used as a technique to swap concerning different IPs based on area.
GlobalSSH presents Free and Premium Accounts. Free ssh account Have got a confined Energetic periode of three days. But, you are able to extend its active time period in advance of it operates out. Premium ssh account will reduce harmony each hour. So, member are necessary to top rated up to start with and ensure the balance is adequate.
But You can even test a Demo Account first just before in fact purchasing it with a certain cut-off date. You can even freeze an account to prevent billing if not use for the next few several hours. Experience free to deal with your account.
SSH tunneling is really a technique of transporting arbitrary networking knowledge above an encrypted SSH relationship. It can be utilized to include encryption to legacy apps. It may also be accustomed to apply VPNs (Digital Private Networks) and obtain intranet companies throughout firewalls.
-*Authorization denied Make sure the consumer attempting to hook up has the necessary permissions to entry the SSH server.
Two-variable authentication is among the most secure SSH authentication method. It involves the user to offer two pieces of knowledge, for instance a password as well as a just one-time code, as a way to log in.
So-termed GIT code readily available in repositories aren’t impacted, Whilst they do include next-stage artifacts allowing the injection in the Create time. From the occasion the SSH 30 Day obfuscated code launched on February 23 is existing, the artifacts within the GIT Edition enable the backdoor to work.
SSH is a typical for secure remote logins and file transfers around untrusted networks. What's more, it supplies a way to secure the information site visitors of any given application applying port forwarding, essentially tunneling any TCP/IP port about SSH.
can route their targeted traffic through the encrypted SSH link for the distant server and access methods on
 Danny Tamberelli Then & Now!
Danny Tamberelli Then & Now! Josh Saviano Then & Now!
Josh Saviano Then & Now! Judd Nelson Then & Now!
Judd Nelson Then & Now!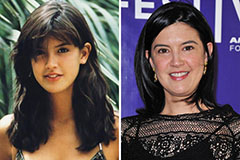 Phoebe Cates Then & Now!
Phoebe Cates Then & Now! Sarah Michelle Gellar Then & Now!
Sarah Michelle Gellar Then & Now!